Extracting data from a running process #Windows / #WindowsSecurity

In this particular instance, I had a long running EXE, that crashed, but didn’t terminate. I couldn’t restart it, but I see that it was still in- memory, so I wanted to see if I could rescue the data from it, or at least some of the data, there was about a 1GB memory footprint.
So, I opened task manager, and Right Click > Create memory dump, and it created a 1GB file. I opened this file in GLOGG, a large file viewer.
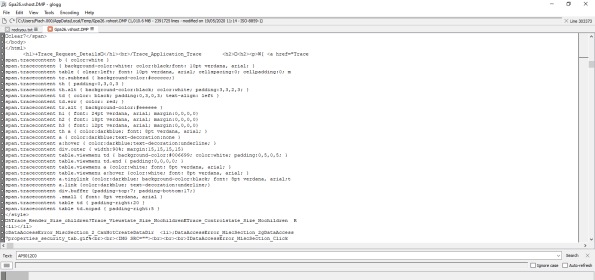
And… lo and behold, amonst alot of binary data, there was plain text, that could be easily extracted. Like in this screenshot, where you can see HTML in plain text.
This also may serve as an alarm bell for any software that might hold passwords or sensitive information in memory. Make sure that passwords are not held in static variables, since this approach could be used to extract them.